
Small and medium-sized businesses continue to have problems shoring up their cyber security. Even with the latest solutions, like antivirus and firewalls, they still need to be wary of impending attacks. New threats are created on a daily basis, all of which want to infiltrate your network and cause harm to your business. In fact, 27.3 percent of all malware in the world was created in 2015 alone. Will we ever escape from the clutches of malware?These results come from PandaLab’s 2015 annual report, which discusses the current state of threats in the online community:
In total, more than 84 million new samples were detected and neutralized by PandaLabs, with an average of 230,000 samples daily. We currently have 304 million samples of malware registered, which means that more than one in four of all samples ever recorded were registered in 2015 (27.36%).
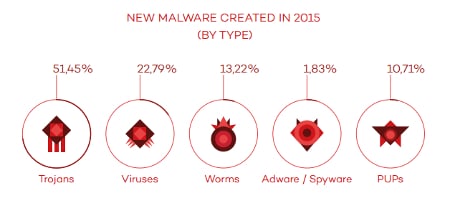
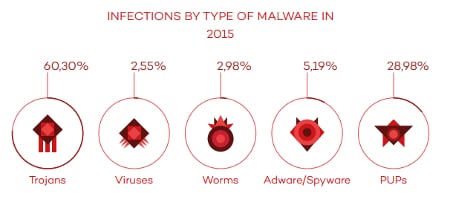
PandaLabs breaks this figure down even further, sorting these threats out by category and infection type:
With so many threats that can potentially infiltrate your system, you need to be extra cautious when using any online technology. It’s now more important than ever before that you ensure the security of your business’s systems. If your organization is infiltrated by online threats, the least of your worries is stolen data; depending on your industry, you could face pricey fines that can break your budget and ruin your reputation. If you store information like credit card numbers and medical records, you’re subject to compliance laws like HIPAA and PCI, which could fine your business an arm and a leg for compromised credentials.
Therefore, as malware grows more powerful, it’s only natural that your business should implement solutions that help maximize your security. As proven by the several high-profile hacks of 2015, your business needs to take cyber security seriously. You simply can’t afford not to do so. Thankfully, implementing security solutions that are designed to mitigate risk is one of K² Technologies’s most valuable IT services. By working with our professional technicians, your business can implement powerful security solutions designed to prevent security discrepancies from becoming full-blown data breaches.
One solution that’s particularly valuable is a Unified Threat Management (UTM) tool. A UTM consists of several enterprise-level security solutions, including a firewall, antivirus, spam blocking, and content filtering. Essentially, the UTM is an all-in-one security measure that helps to prevent issues from spiraling out of control. Granted, it isn’t possible to find a one-size-fits-all solution that fits for every single business, so it’s recommended that you contact K² Technologies for an IT consultation. We’ll help you determine the best way to protect your business.
For more information or assistance with cyber security, contact K² Technologies at 307-686-3025.

 Mon-Fri 9 AM to 5 PM Mountain
Mon-Fri 9 AM to 5 PM Mountain 888-686-3025
888-686-3025



