Small Business Tech Security Small businesses need to take cyber security seriously, preventing lapses or weak poin...

What You Need to Know About Android Malware Hackers are devising new ways to infect phones with malware. Learn abou...
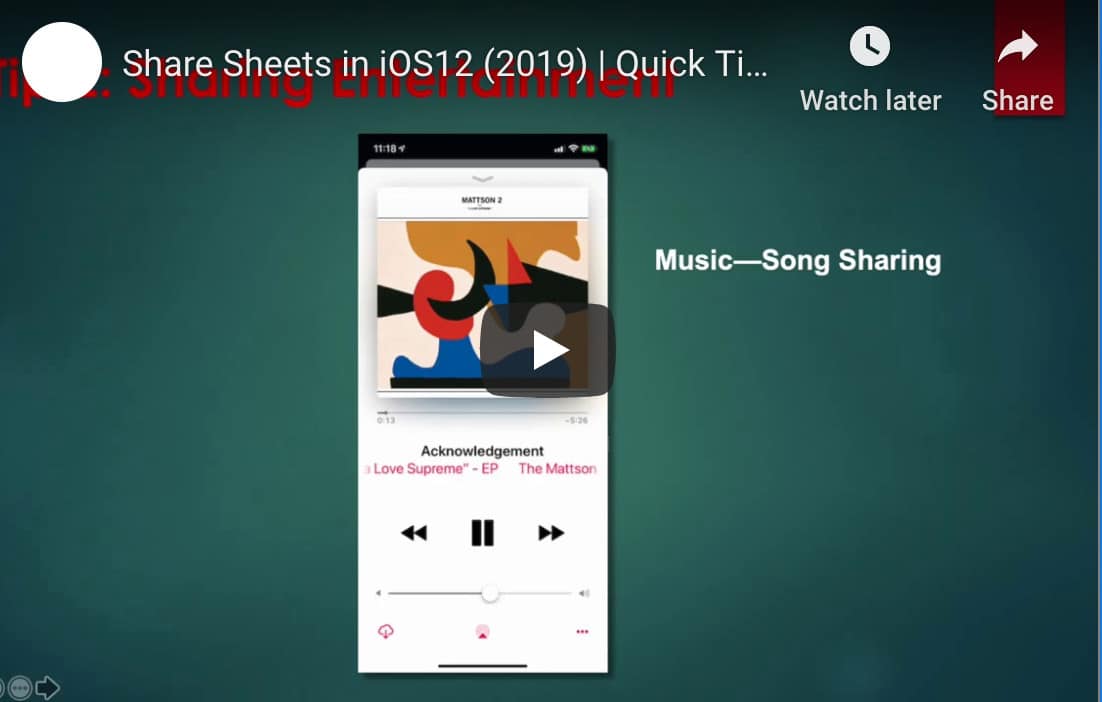
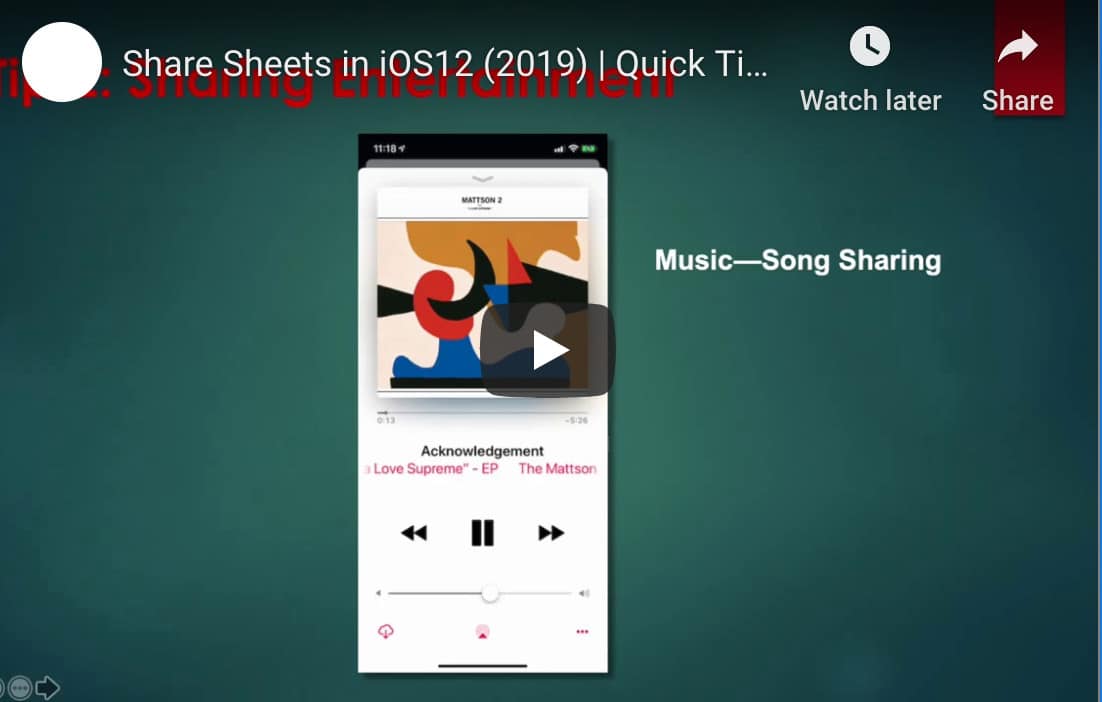
How to Use iOS12 to Instantly Share Information With Colleagues Want an easier way to communicate with your colleag...
Downloading Apps on Your Android Device: How to Use Your Computer Installing apps to your Android phone via your de...

Will Your Business Be Impacted by the End of Microsoft Exchange 2010? Exchange 2010 has been a great program for bu...

Protecting Your Data from SHTML Phishing Data security is vital to any business. Learn how SHTML phishing works and...

What Is the Dark Web and How Can You Stay Off It? Ever heard of the dark web? It’s definitely not a place you want ...

Capital One Data Breach Affects More Than 100 Million Customers and Small Businesses in The U.S. & 6 Million in...

The cloud may still feel like a new technology – but in reality, it’s been around for more than 10 years now. Does ...

Phishing Attacks Target OAuth Credentials to Gain System Access Discover how an increasingly popular authentication...

5 Incredible Benefits of Effective Managed IT Services Managed IT services are one of the many ways an organization...

What Is Network Segmentation? Businesses that offer WiFi to their customers or have sensitive data needs should con...